Updated on by Nic Butler
Over the last few years, conversational AI has gone from experiment to infrastructure. It now sits at the centre of how many companies support customers, run internal operations, and expose core systems. That shift brings real value-but it also changes the risk profile.
As a CTPO, one pattern I see again and again is this: agents are given more data access than they actually need. Not because teams are careless, but because limiting access is hard to do well. And when it’s hard, the fastest way to success is “just give it access”.
The answer isn’t to slow innovation or restrict agents to the point they become useless. The answer is data minimisation, done properly, with tooling that makes targeted access the default rather than the exception.
Why Data Minimisation Matters
Data minimisation is often framed as a compliance checkbox. In reality, it’s a design principle-and a practical one.
Regulations like GDPR and CCPA demand data minimisation, but even if they didn’t, limiting data exposure is still desirable. Every extra dataset an agent can see increases the fallout from a mistake, a bug, or a breach. There’s also a performance angle that doesn’t get talked about enough. Agents work better when they’re not burdened with irrelevant context. When the scope is narrowed, you get faster responses, clearer reasoning, and fewer unexpected behaviours or hallucinations.
And finally, there’s trust. Customers may not see your architecture, but they feel the outcomes. When systems behave predictably and respectfully with their data, confidence follows.
Targeted Access: A Better Way to Think About Agent Permissions
Most agents don’t need broad access. They need specific access, in a specific moment, for a specific reason. A billing agent doesn’t need a full customer profile. A support workflow doesn’t need analytics data. Access should be tied to intent, not convenience.
That’s where targeted access comes in. Instead of static, all-or-nothing permissions, access is scoped by role and refined by context. What data is needed for this task, right now?
Just as importantly, access should be observable. If you can’t answer “what did this agent see, and why?” you don’t really have control-you have assumptions. When done well, targeted access reduces risk without slowing teams down. In fact, it usually does the opposite.
How Cyclr’s MCP PaaS Makes This Practical
This is one of the problems Cyclr’s MCP PaaS is built to solve.
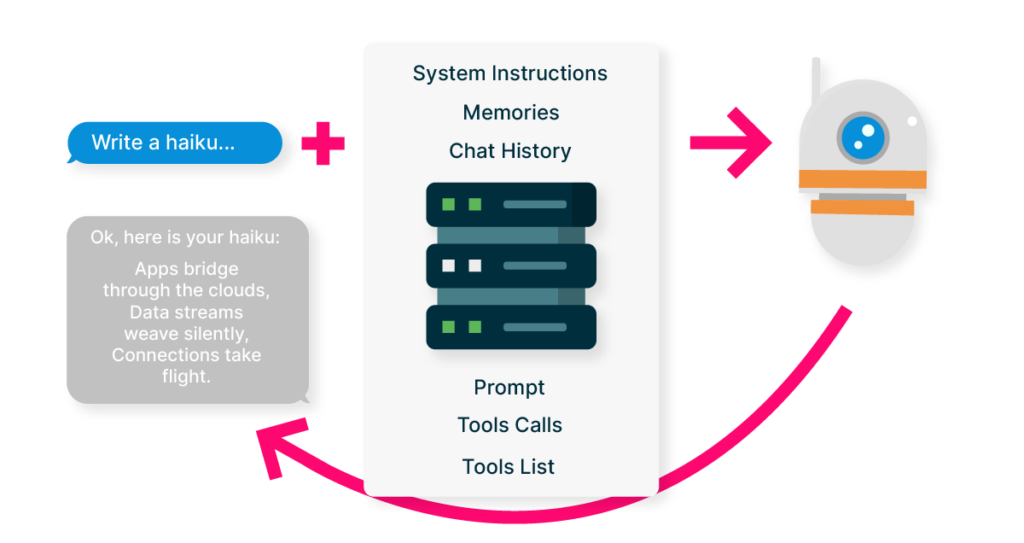
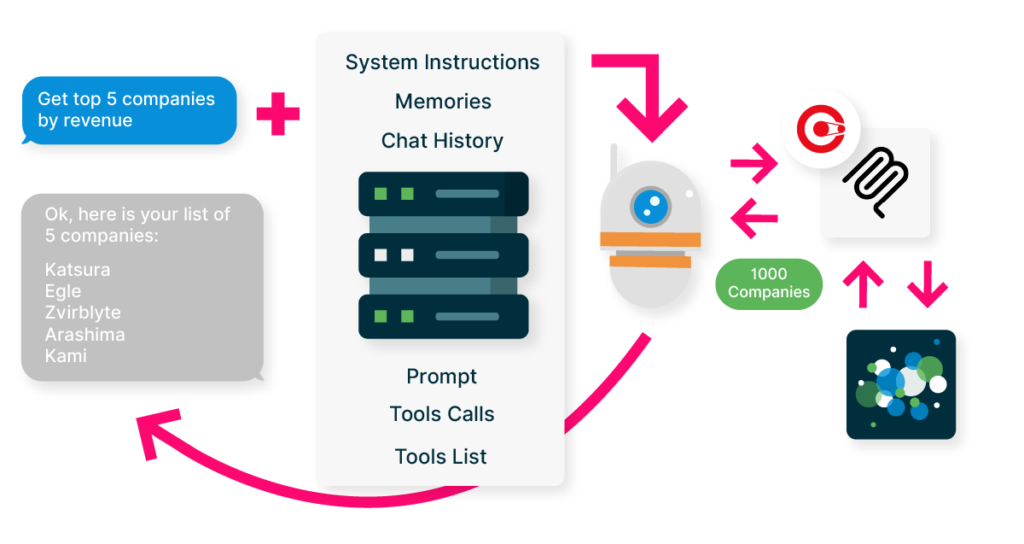
At its core, the platform enforces fine-grained access controls that operate at the level agents actually work at: fields, records, and datasets, not just systems. Data is delivered dynamically, based on context and scope, rather than pre-exposed “just in case” so agents only see what’s relevant to the task they’re performing, and nothing more.
Further options like post-retrieval scripting and data orchestration flows can allow fine grain, explicit data filtering and minimisation before the context leaves the platform. This is vital for shaping the context before it leaves the data source. Operations like sensitive data redaction, over-retrieval trimming, and merging the data from many sources to alleviate the AI having to make multiple calls are all imperative to keep data to a minimum and fully control what the Agents have access to.
Discover Cyclr’s MCP PaaS
The Agentic framework is the new standard, discover how to move beyond custom API wrappers and establish your SaaS as an AI-Ready Platform.
Why Wait? Accelerate your AI Roadmap in Days, not Quarters.
SaaS companies are in full control of the methods that are available to AIs and Agents. Multiple MCP servers can be created to contain logically grouped tools that are individually available and securable ensuring only the right AI gets the right tools to interact with. The single pane of glass control surface gives immediate and realtime views on the requests that LLMs and Agents are making, what data is being returned and to where.
Every access is logged. Every decision is auditable. And because MCP PaaS sits between agents and data sources, these controls can be applied consistently across existing systems without major re-architecture. The goal isn’t to wrap AI in red tape, it’s to make the safest path the easiest one.
Minimising Data Without Limiting Capability
Data minimisation doesn’t make agents weaker. It makes them more reliable.
When access is intentional, scoped, and transparent, teams move faster. Security teams sleep better. Compliance stops being a last-minute scramble. And customers trust the systems they’re interacting with.
Agentic access should be treated no differently to your API access controls. This is no longer optional, as AI agents become more capable, the question isn’t whether to limit data access, it’s whether you can do it in a way that still offers flexibility and value to your customers.
MCP PaaS exists to make that balance achievable.
Discover how companies in your SaaS space are adapting to MCP
With increasing demand from users to be able to access their data directly through AI chat platforms, B2B SaaS companies are beginning to launch their own MCP strategies.
But how do you decide what functionality to make available via AI?
This is why we have researched over 800 B2B SaaS companies, ranging in size, vertical focus and growth stage to create a dataset of who is building what (and who is yet to implement a native MCP solution).
The tool below enables you to select a SaaS vertical category to see actual MCP use cases that have been implemented, also enabling you to see who has implemented it.
Discover Cyclr’s MCP PaaS
The Agentic framework is the new standard, discover how to move beyond custom API wrappers and establish your SaaS as an AI-Ready Platform.
Why Wait? Accelerate your AI Roadmap in Days, not Quarters.